Borderpoint Cyber Protection
Welcome to Borderpoint – A dedicated managed cybersecurity service that monitors your IT infrastructure, detects vulnerabilities and threats, intrusion attempts, security anomalies, badly configured applications and unauthorised user activities.
Systems-driven alerts are investigated by Fresh Mango security analysts who escalate identified threats and provide guidance on remedial actions required to mitigate those threats.
THE ISSUE
an average of 146 days. You must be on the constant lookout for security threats lurking in your
network traffic – managed detection and response gives you actionable insight when it counts.
Cybercriminals are getting more sophisticated with attackers conducting in-depth reconnaissance to find vulnerabilities before launching their attack. Firewalls, anti-virus, and patching are often not resilient enough to protect your IT from being compromised. As illustrated above, often once a breach occurs cybercriminals have access to a network for long periods of time without the breach being discovered.
To combat this increased level of threat larger companies, have been deploying managed detection and response capabilities. This is achieved by either operating an in-house SOC (security operations centre) which is expensive to set up and operate or by commissioning a managed service like BORDER POINT which has been designed and built to provide an affordable solution to businesses of all sizes.
WHY Phoenix Caribbean?
The Borderpoint Security Operations Centre (SOC) is operated by experienced cyber security analysts overseen by James Griffiths and Dave Woodfine; both of whom have extensive experience in setting up and operating SOC monitoring services for large corporate organisations including the MOD and the Bank of England.
The BORDER POINT service has been designed and built based on experience gathered working for organisations where the highest standards of security are demanded.
Check our Borderpoint Service!
INCIDENT DETECTION & BORDERPOINT RESPONSE
Activity and Security analysis
Intrusion Detection
Flexible Incident Response
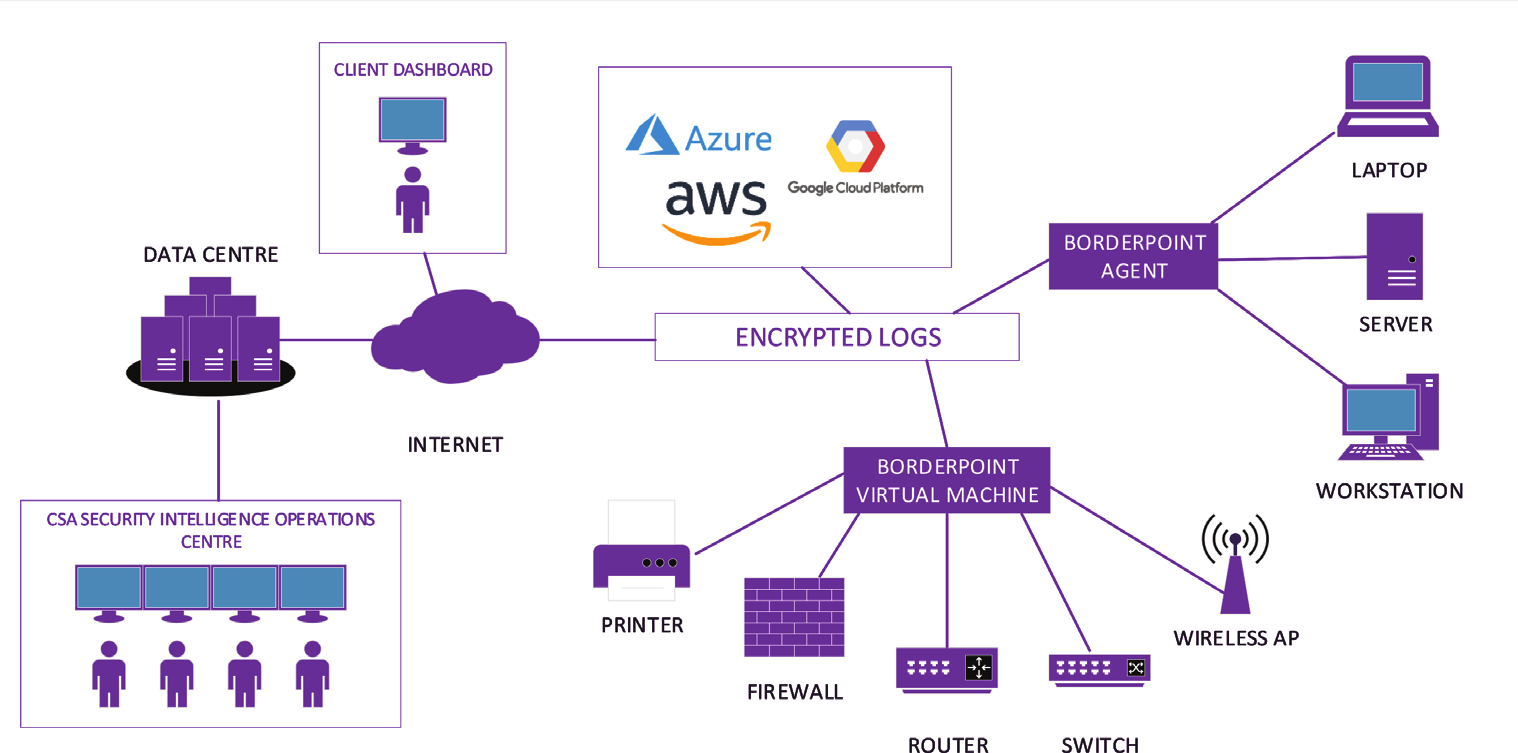
BORDERPOINT collects system and security data from your IT devices (on-site or cloud) and then forwards it securely to Phoenix Caribbean. This data is indexed and analysed against bespoke rule-sets and a threat intelligence database to identify potential threats, behavioural anomalies and to detect intrusions.
BORDERPOINT SECURITY HEALTH & MONITORING
Software Audit
Vulnerability Assessment
File Integrity Monitoring
Security Configuration Assessment
BORDERPOINT will conduct a full software audit every 12 hours on each monitored device. This inventory check will provide a detailed list of all software installed including patching status. This near real-time service will provide assurance that you understand what software has been legitimately installed on your devices and will be used to inform the BORDERPOINT vulnerability assessment service.
BORDERPOINT REPORTING & COMPLIANCE
Regulatory Compliance
User Dashboards
BORDERPOINT alerts and reports against compliance with some of the mandatory security controls for various industry standards and regulations. BORDERPOINT is configured and mapped to the technical controls of the PCI DSS (Payment Card Industry Data Security Standard), GDPR, NIST and HIPPA. Additionally Phoenix Caribbean are working on the technical controls for the Cyber Essentials accreditation and ISO 27001.
FAST & SIMPLE DEPLOYMENT
A fast and easy deployment straight onto your IT. For windows, BORDERPOINT can be automatically deployed through group policy deployment or an installer for singular hosts. For Linux and MacOSX a simple installer script is provided. As part of the installation process, our deployed agent will register with the BORDERPOINT management server ensuring the BORDERPOINT service is up and running straight away without the need for license keys or software downloads.
For log sources where the BORDERPOINT endpoint agent can’t be installed (firewalls, routers, switches) the BORDERPOINT on-premise pre-configured Virtual Machine can be deployed onto your infrastructure. Once the Virtual machine is up and running then any remaining devices will also be monitored. All you need to do is to install and power on and let BORDERPOINT do the rest.
TECHNICAL SPECIFICATION
AIX 5,6 and 7
Amazon Linux, Amazon Linux 2
CentOS 5,6 and 7
Debian 7 and above
Fedora 22 or above
HP-UX 11.31
MacOSX Sierra or above
OpenSUSE
Oracle Linux 5,6 and 7
Solaris 10 and 11 – i386 / sparc
Suse 11 and 12
Ubuntu 12.04 and above
Windows XP Service Pack 2 and above
Windows Server 2003 and above
BORDERPOINT Encryption
All BORDERPOINT logs are sent from the monitored device to the processing manager using AES 256 bit encryption via either UDP or TCP.
Installation
The BORDERPOINT agent can be installed using both .msi for Windows based operating systems and .sh command line script for *nix based operating systems. A full installation guide is provided if required. The agent install is fully automated and will automatically register with the BORDERPOINT service.
ADDITIONAL Phoenix Caribbean SERVICES
Providing around the clock managed cyber services from the SIOC from a team of Cyber professionals.
Our range of security assessments cover both technical and operational aspects for any business
Phoenix Caribbean produces its own and re-sells a number of specialist cyber products.
Our crisis response service is run through the SIOC providing a number of services to help companies when something goes wrong.
Phoenix Caribbean provides a range of cyber training services designed to meet your needs.
The Senior Team at Phoenix Caribbean provide a range of cyber consultancy services to assist companies to understand cyber security
CONTACT US:
If you would like more information or would like to request a demonstration of the BORDERPOINT managed service then please contact us via:






